Loubby AI Data Protection & Privacy Policy
Last Updated: 28th August, 2025
Purpose. This policy sets out Loubby AI’s governance, controls, and commitments for protecting personal data and other confidential information throughout its lifecycle. It is intended for customers, candidates, end‑users, partners, employees, contractors, regulators, and auditors. This document also serves as Loubby AI’s public‑facing privacy notice and internal standard for implementing privacy by design.
Scope. Applies to all Loubby AI legal entities, employees, contractors, and systems globally; to all personal data processed in connection with Loubby AI products and services; and to confidential business information handled on behalf of customers. Where local law is stricter, local law prevails.
Status. Approved by the Executive Team and the Data Protection Officer (DPO). Effective: 27 Aug 2025. Review cadence: at least annually and upon material change.
1) Key Definitions (plain‑English)
- Personal Data: Any information that relates to an identified or identifiable person (e.g., name, email, online identifiers, device IDs, voice/video, CV/resumé data, HR data, support transcripts, usage logs).
- Special Categories: Sensitive data requiring higher protection (e.g., health, biometric identifiers, racial/ethnic origin); Loubby AI does not intentionally collect these except where legally required and consented, or where a lawful exemption applies.
- Processing: Any operation performed on data (collection, recording, storage, use, disclosure, deletion).
- Controller / Processor: Loubby AI may act as controller (e.g., website, marketing, HR) or processor for Customer Data processed under a services agreement and Data Processing Addendum (DPA).
- Customer Data: Content and personal data that customers upload or generate in Loubby AI services.
- Anonymization: Irreversible removal of identifiers. Pseudonymization: Replacing identifiers with code keys stored separately.
2) Governance & Accountability
- Leadership: A named Data Protection Officer (DPO) oversees compliance (contact in §17). An internal Privacy Steering Committee (Legal, Security, Product, HR, Engineering, Support) meets quarterly and on demand for high‑risk matters.
- Policies: This policy is supported by: Information Security Policy, Secure SDLC, Vendor Risk Management, Incident Response Plan, Business Continuity & Disaster Recovery (BC/DR), Access Control Standard, Data Retention Schedule, and Acceptable Use.
- Records of Processing Activities (RoPA): Maintained for controller and processor operations, including purposes, categories, recipients, international transfers, retention, and safeguards.
- Training: Role‑based privacy and security training at hire and annually; targeted refreshers for engineers, support, talent/recruiting, marketing, and sales.
- Privacy by Design: DPIAs are performed for new and materially changed features, especially those involving AI/ML, large‑scale profiling, biometric/voice/video analysis, geolocation, or cross‑border transfers.
3) Principles We Follow
- Lawfulness, fairness, transparency
- Purpose limitation and data minimization
- Accuracy
- Storage limitation (keep only as long as needed)
- Integrity and confidentiality (security by default)
- Accountability (we document and can demonstrate compliance)
4) Lawful Bases & How We Use Data
Depending on the context, we rely on:
- Performance of contract: to deliver our products, support, and billing.
- Legitimate interests: to secure, improve, and personalize services; prevent abuse; measure performance; B2B marketing to business contacts where permitted (with opt‑out at any time). We conduct balancing tests where required.
- Consent: for optional features (e.g., marketing subscriptions; certain cookies; use of recordings/transcripts for quality/training where applicable). Consent can be withdrawn.
- Legal obligation: to comply with tax, accounting, and regulatory requirements.
- Vital/public interest: rarely, e.g., to prevent serious harm.
Illustrative purposes (non‑exhaustive):
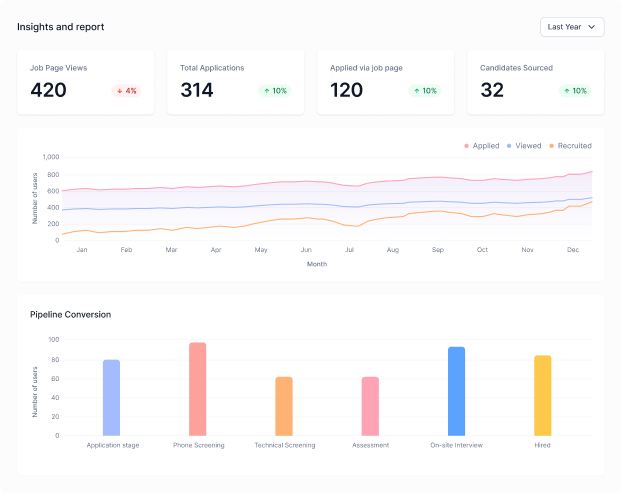
- Account creation and authentication; team administration; usage analytics; fraud/abuse detection; customer support; product research and improvement; recruiting and candidate evaluation; partner and vendor management; compliance and auditing.
5) Categories of Data We Process
- Identity & contact: names, emails, phone, addresses, employer, role.
- Account & usage: credentials, access logs, device/browser metadata, feature usage, event telemetry.
- Content: prompts, files, code, transcripts, annotations, feedback.
- Payments & billing: transaction details (card data handled by certified payment processors; we do not store full card numbers).
- Support & communications: tickets, chat, email, call recordings (where allowed and disclosed).
- Recruiting/HR (if you apply or work with us): CV/resumé, work history, assessments/interviews (including optional AI‑assisted interview tools), background‑check results where legally allowed, visa/work authorization.
- Sensitive data: avoided by design; if provided by you or necessary by law/contract, we apply enhanced safeguards and minimize processing.
6) AI/ML, Model Training & Human Review
- Customer Data in paid/workspace products is not used to train foundation models unless a contract or in‑product setting expressly allows it (opt‑in by default). Aggregated/anonymized statistics may be used for service improvement.
- Consumer/website inputs may be used to improve safety and quality only as disclosed at the point of collection and subject to opt‑out mechanisms where available.
- Human review for quality/safety is restricted, role‑based, logged, and subject to confidentiality and access controls.
- Automated decision‑making: We do not make solely automated decisions that have legal or similarly significant effects without appropriate human oversight and the ability to request review.
7) Security Measures (Overview)
Security is handled jointly by Security Engineering and IT under the CISO, aligned to recognized frameworks (e.g., ISO 27001 and NIST CSF). Loubby AI does not currently hold SOC 2 certification and is actively pursuing SOC 2 compliance; we are undergoing a SOC 2 gap analysis and preparedness/readiness phase. Controls include:
- Encryption: TLS in transit; encryption at rest for primary data stores and backups; managed keys and key rotation; secure secret management.
- Access controls: SSO/MFA, least privilege, role‑based access, JIT access for support. Quarterly access reviews.
- Network & platform: hardened baselines, segregated environments (prod/stage/dev), firewalls/WAF, endpoint protection, vulnerability scanning, patching SLAs, penetration testing.
- Application security: secure coding standards, code review, dependency scanning, SAST/DAST, supply‑chain integrity (SBOM where applicable), change management, secrets scanning, CI/CD controls.
- Monitoring & logging: centralized logging, alerting, intrusion detection, anomaly detection, anti‑abuse and rate‑limits.
- Resilience: regular backups, tested restores, RTO/RPO objectives defined per service tier, BC/DR plans with at least annual exercises.
- Physical: trusted data centers/cloud regions with certified controls; badge‑based office access; visitor management.
Certification status: As of 27 Aug 2025, Loubby AI is not SOC 2 certified. We align our controls to leading frameworks and are actively pursuing SOC 2 compliance; we are currently undergoing a SOC 2 gap analysis and preparedness/readiness phase with independent assessors. Audit artifacts (e.g., security overview, penetration‑test summary) can be provided under NDA.
8) Sub‑Processors & Vendors
- We maintain a current list of sub‑processors used to deliver our services (infrastructure, analytics, support, communications, payments). For processor activities, we enter into a DPA with each vendor, ensuring confidentiality, security, and transfer safeguards.
- We perform risk‑based due diligence (security/privacy questionnaires, certifications, TIAs for international transfers, contract review) and re‑assess at least annually.
- Customers may subscribe to change notifications where available; material changes that affect processing or transfer risks are communicated in advance where required.
9) International Data Transfers
We use regional hosting and data residency options where feasible. Where data is transferred internationally, we implement recognized mechanisms (e.g., EU Standard Contractual Clauses with required Annexes; UK IDTA/UK Addendum; adequacy decisions such as the EU‑U.S. Data Privacy Framework and the UK‑U.S. Data Bridge where applicable). We also conduct Transfer Impact Assessments (TIAs) and implement supplementary measures as needed.
10) Retention & Deletion
- We retain personal data only for as long as necessary for the purposes stated, to meet legal/accounting requirements, or to resolve disputes. Retention is governed by our Data Retention Schedule (Appendix A). When a retention period ends or upon validated deletion request, data is deleted or irreversibly anonymized. Backups age out per the backup rotation schedule.
- Customer‑managed deletion: Workspace owners/admins can delete content and users through in‑product controls. Certain immutable logs may persist for security/audit purposes for limited periods.
11) Your Privacy Rights & How to Exercise Them
Depending on your jurisdiction, you may have the right to access, correct, delete, restrict, object, portability, and to opt out of targeted advertising, sales, or profiling. You also have the right to withdraw consent and appeal denials where applicable.
How to submit a request
- Use our Privacy Request Portal or email listed in §17. We will verify identity (and authority for agent/enterprise requests) and respond within the timelines required by law. We will not discriminate for exercising your rights.
- For requests made through an enterprise account, we may redirect you to your organization’s administrator where the organization is the controller.
12) Cookies & Similar Technologies
We use strictly necessary, functional, performance/analytics, and (where applicable) advertising cookies. You can manage preferences via our Cookie Banner/Settings and browser controls. See our separate Cookie Policy for details.
13) Children & Teens
Our services are not directed to children under the minimum age required by local law (e.g., 13–16). We do not knowingly collect their data without appropriate consent. If we learn we have, we will promptly delete it.
14) Incident Response & Breach Notification
We operate a 24×7 incident response program with documented runbooks. Suspected incidents are triaged, contained, eradicated, and remediated. We notify customers and, where required, regulators and affected individuals without undue delay and within the timeframes set by applicable law. We maintain evidence, lessons learned, and post‑incident reports.
15) Product‑Specific Disclosures (examples)
- AI interview/voice or video features (if enabled): We will provide clear, context‑specific notices explaining what is captured, how long we keep it, and how to opt out or use non‑recorded alternatives. Transcripts may be available to authorized reviewers at your organization; human review for quality/safety may occur under strict controls and NDAs.
- Integrations & APIs: When you enable third‑party integrations, data may flow to those providers under their own privacy terms. Review vendor policies before enabling.
- Payments: Processed by PCI‑compliant providers. We do not store full payment card data in our systems.
16) Enterprise & B2B Marketing
- We may send service and transactional emails (e.g., security, billing, critical product updates). You cannot opt out of strictly necessary service messages.
- Marketing communications are consent‑based where required. You can unsubscribe at any time via the link in the email or from settings.
- We maintain suppression lists to honor opt‑outs.
17) Contact, DPO & Complaints
- Controller: Loubby AI, [Registered Address], [Country]
- EU Representative (if applicable): [Name, Address, Email]
- UK Representative (if applicable): [Name, Address, Email]
- DPO: [Name], dpo@loubby.ai (or privacy@loubby.ai)
- Privacy Requests: privacy@loubby.ai or the Privacy Request Portal.
- You can also lodge a complaint with your local supervisory authority. We welcome the chance to resolve concerns first.
18) Changes to this Policy
We may update this policy to reflect operational, legal, or regulatory changes. We will post updates with a new effective date and, where changes are material, provide additional notice (e.g., email or in‑product).
Appendices (Binding)
Appendix A – Data Retention Schedule (baseline; subject to legal holds)
Note: Specific customer‑contracted retention controls prevail if stricter.
Data Category | Baseline Retention | Notes |
Account profile (admins/users) | Active use + 24 months | Delete within 90 days after termination unless required for legal/audit. |
Authentication logs | 12–24 months | Shorter where feasible; security investigations may extend. |
Application/content data (workspace) | Customer‑configurable | Deleted on workspace deletion or per admin action; backups age out per rotation. |
Payment/billing records | 7–10 years | Per tax/accounting laws. |
Support tickets & call/chat recordings | 24 months | Redacted where possible; sensitive content discouraged. |
Marketing contacts | Until opt‑out or inactivity 24 months | Honor unsubscribe immediately; retain minimal suppression data. |
Recruiting/candidate data | 12–24 months (country‑specific) | With consent extensions where permitted. |
Appendix B – Security Controls Mapping (summary)
- Identity & Access: SSO/MFA, RBAC, device posture checks for privileged roles, quarterly reviews.
- Data Protection: encryption at rest/in transit; pseudonymization for analytics; key management; secure deletion.
- AppSec: SDLC, code review, SCA, SAST/DAST, secrets scanning, pentests at least annually; bug bounty or responsible disclosure.
- Ops: change management, backup/restore testing, capacity planning, DR exercises, monitoring and alerting.
- Endpoint/IT: EDR, disk encryption, patch compliance, phishing defense, removable media controls.
Appendix C – Data Subject Rights (process overview)
- Intake via portal/email; confirm receipt (within 10 business days where required).
- Verify identity/authority; log request in RoPA/DSR register.
- Triage (access/correct/delete/opt‑out/portability/restriction/appeal).
- Fulfil within statutory timelines; document exemptions/denials with reasons.
- Provide response securely; record closure and metrics; implement learnings.
Appendix D – International Transfers
Preferred: regional processing and storage. Where cross‑border transfer is necessary, we use recognized mechanisms (SCCs, UK IDTA/UK Addendum, adequacy decisions like EU‑U.S. DPF/UK‑U.S. Data Bridge), maintain TIAs, and apply technical/organizational supplementary measures (e.g., encryption, access controls, minimization).
Appendix E – Sub‑Processor Management
- Maintain a public sub‑processor list with purpose and location.
- Contractual DPAs with confidentiality, security, audit rights, onward‑transfer restrictions, and incident notice obligations.
- Pre‑engagement due diligence; annual reassessment; change notifications with opportunity to object where required.
Appendix F – DPIA & TIA Triggers
New large‑scale processing; profiling impacting individuals; automated decision‑making with significant effects; processing of special categories; monitoring public areas; cross‑border transfers to non‑adequate countries; new sub‑processors handling sensitive roles.
Appendix G – Incident Notification Templates (controller & processor)
- To customers: summary of incident, data types, impact, containment, mitigations, recommended customer actions, contact, and updates cadence.
- To regulators: timeline of awareness; nature of incident; categories/volume; likely consequences; measures taken; DPO contact; cross‑border effects.
- To individuals (if required): plain‑language description, what happened, what we are doing, what you can do, and help resources.
Appendix H – Product‑Level Notices (to be hosted in Help Center)
AI model usage and training toggles; human review disclosures; data residency; logs/telemetry categories; retention settings; export/deletion self‑service; integration‑specific data flows.
Implementation Checklist (Internal)
- Publish public sub‑processor list and email subscription for updates.
- Stand up Privacy Request Portal; implement identity verification and case management.
- Finalize DPA (controller↔processor) with SCCs/UK addendum annexes and security schedule.
- Maintain RoPA; complete DPIAs/TIAs where required.
- Configure data retention in prod systems; verify deletion workflows and audit logs.
- Run tabletop for incident response; validate 24×7 on‑call; prepare notification templates.
- Confirm cookie consent and preference center across web properties.
- Train staff; document “privacy by design” in SDLC gates.
Note to readers: This policy is comprehensive by design. Some controls vary by product tier, deployment model, or customer configuration. Contractual terms (e.g., Master Services Agreement and DPA) prevail in case of conflict. For questions, contact the DPO in §17.